Hello, I am Thijs and I have a problem: I keep buildings things. Silly things. Things that I am sure nobody else will ever use. And yet I keep building them (and release the source code). Why? Because I love it so much. Because I keep thinking of cool use-cases for linking things together.
My story starts in the summer of 2013. I wanted to found a game studio and I had a brand new, original idea for an amazing game: Kahoot. Or… well… our version was called ‘Quizted’ and was aimed towards gamers instead of educators, but the main premise was the same: an audience participation game around quizzing. (Let me spare you the googling: Kahoot beta was released later that year).
I managed to secure some money from the Flanders Audiovisual Fund (VAF) and in the summer of 2014 I hired 3 of the worlds best programming… students. Two software developers (Katia & Yannick) and one marketing student (Ken). Second years students, looking for a summer job. I also hired a consultant from Portugal who would be working on the quiz editor.

By the end of summer, we had a pretty basic proof of concept: we had systems in place to create quizzes, play these quizzes with up to around a hundred people, and I had even developed a rudimentary licensing system to accept online payments. Ken had been working on a crowdfunding campaign and we organised a few ‘quizwitz viewing parties’ where we would play the game with a group of people. I hacked together a QuizWitz mod that allowed a ‘quizmaster’ to control the pace of the game and added a jury mod that allowed manual correction of open ended questions… and our QuizWitz Live events were born. And thus we started our transformation from a gaming studio to an event organiser.

I split up the organisation and moved the event management side into a separate entity (Bektoe vzw, more commonly known as De Quizfabriek). More people joined and we started disrupting the Flemish quiz space with our digital quiz experience™. I would be in charge of the quiz software (through my own company), the content would be provided by our fellow members.
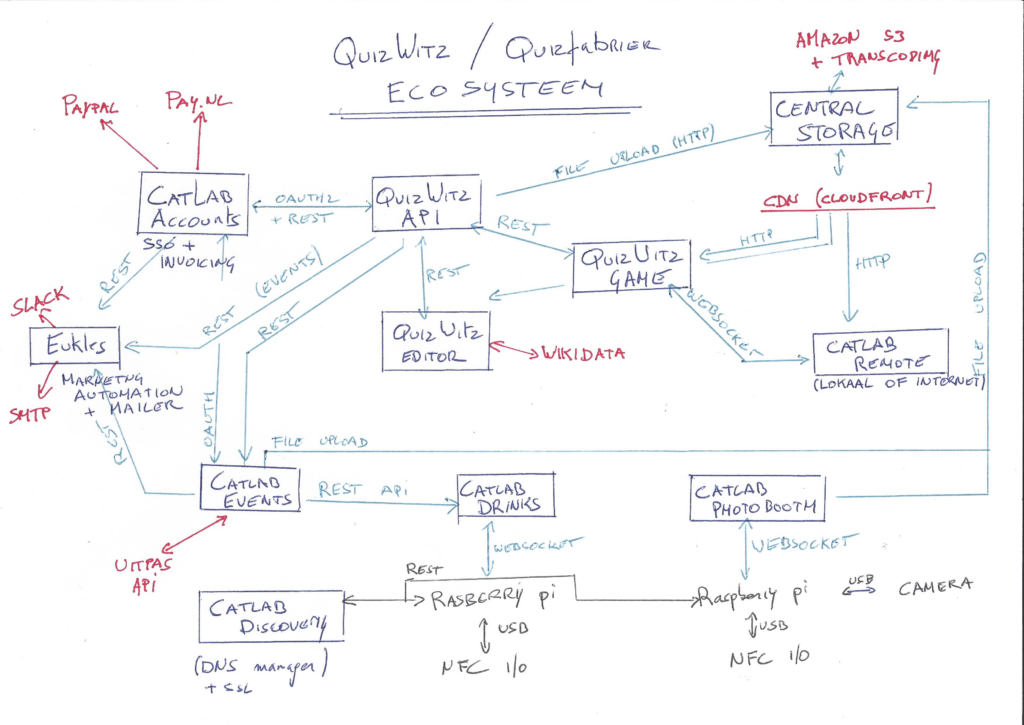
It’s all fun and games … until someone has a new idea. And there were ideas. Tons of ideas. Initially we sold ticket through an online form and quizteams had to pay their entrance fee at the door. Due to a whole bunch of no-shows, I replaced that with an online registration system: CatLab Events was born (source code on github). And since we wanted to support the UitPAS program, obviously that had to be integrated as well.
In 2019 our events started to grow unwieldingly large and we started having trouble with handling the bar. It’s not a great expience if you need to wave for ten minutes until a server notices you and then has to disturb the people around you by taking your order. So I wrote a very simple QuizWitz mod that would allow players to order drinks from their table. CatLab Drinks was born (source code available on github).
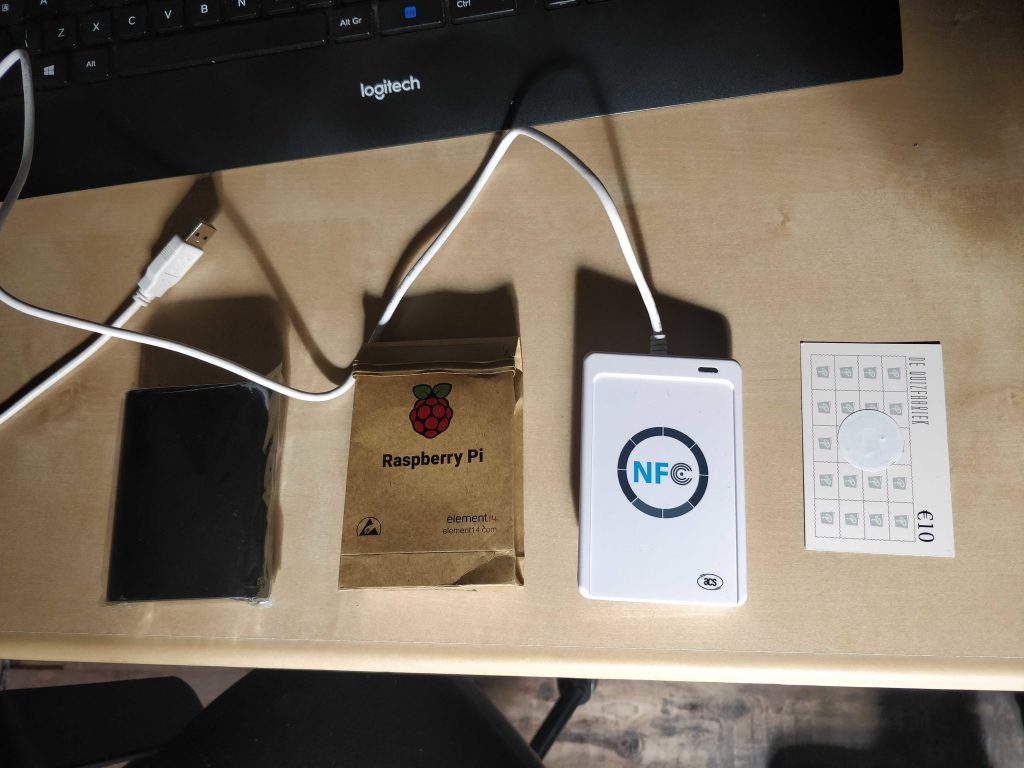
Everything ran smoothly from their on… until I wanted to experiment with digital drink vouchers. Up until then we had been working with the traditional paper drink vouchers had to be purchased at a central cash registry, but that all felt a bit backdated. So I extended CatLab Drinks to be able to connect to a Raspberry Pi (over websocket) to a service that provided NFC reader/writer capabilities. One of the bigger challenges was that I wanted to store the user credit on the cards themselves, so I would be able to read (and change) the balance even if the central system would go down.
We started a few phased release tests but ultimately started using the system for all our events. I also extended the app even more to allow players to popup their cards using a QR code on the back (resulting in a whole bunch of synchronization challenges that had to be handled every time a card was read or written) and instant payment of remote orders so that servers could just rely on the system instead of manually scanning the cards. Challenge completed. Next!
At one of our themed quizzes we wanted to add a photobooth where players could take a team picture (source code available on github). Taking the pictures was easy, but keeping track of who was on the picture provided to be a challenge. But a solution was at hand! Since every team already had an NFC card, it would be trivial to make a small Raspberry PI based system where players would scan their NFC card and a picture is taken automagically.


But a new problem popped up: the NFC cards were basically anonymous and some teams even used the same card for multiple events. So I had to extend CatLab Drinks even more, to be able to check players in and connect their card to their name and email address. Then I just had to provide an API for the photobooth application, connect the whole bunch up to Eukles (my marketing automation system that also handles all communication from QuizWitz and the ticketing system) and bam, photos were automatically emailed to the players.
Oh, and also all assets, photos, video fragments, etc are stored in a central storage system that makes sure that no duplicate data is stored (source code available on github).
Oh, and I also have a laptop that listen to a datastream (websocket) and emits MiDI signals on certain game events to a digital lighting console to control the theater lights over DMX. But that is not included in the overview.
And that is basically what our system looks like. From registering for our events, over checking in and playing, to checking your score on our website when the game is done… An ecosystem of overengineererd madness… But so much fun to build. I’m trying to cut back on new ideas and perhaps properly document what has already been created. Maybe someone on GitHub can see some use of projects after all…
But what if, instead of a quiz, we would gather with 160 players to play a digital escape game…